Mr. J, a Former Professor Series – Entry 51: To Johnston
To Johnston,
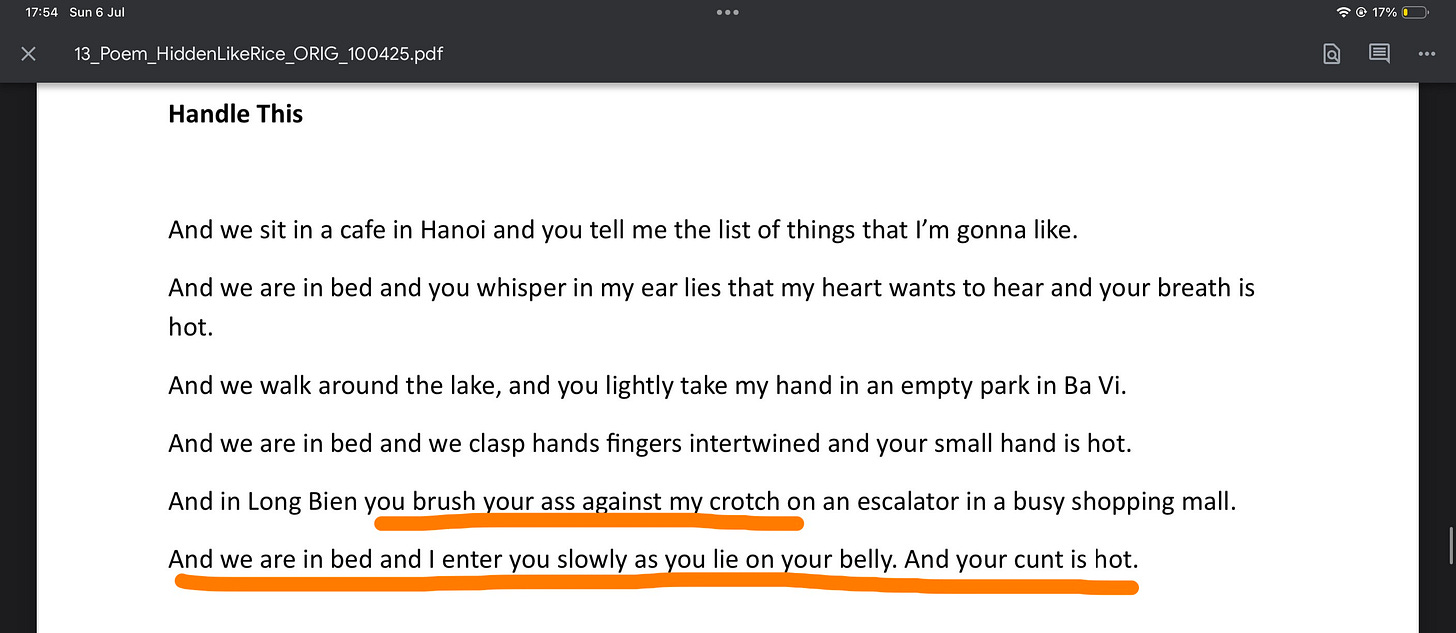
I wonder — when you crafted your so-called “poetic tributes,” did you ever imagine your daughter reading them?
Did you ever pause to think how it might feel to watch her father turn another woman’s body into a metaphorical playground — a stage for grief fantasies and symbolic power games?
Did you ever consider what it might do to her sense of trust, to her image of you as a father?
Or is that a boundary you reserve only for your own narrative safety, not for the emotional safety of those around you?
When we choose to describe someone else’s most private details without consent, we don’t just cross their lines. We show the world how we might treat every relationship — including those we claim to protect the most.
So I wonder: if your daughter read this, would she call it art? Or would she call it what it truly is — an act of narrative violence dressed in metaphor
Would you call it art if someone described your daughter’s intimate body without her consent, the way you did mine?
Written without consent. Screenshot retained for documentation purposes. Originally authored by Pat Johnston.
If you truly don’t care about your daughter being described that way, you’ve already answered every question about your capacity for intimacy and protection — or the lack of it.
Update (June 10, 2025): Counter-Takedown Filed — Fair Use & Survivor-Led Documentation
On June 9, I received a formal DMCA notice from Google informing me that Patrick Johnston had submitted a copyright takedown request targeting my publicly accessible survivor evidence folders documentation already submitted to QPS as part of police evidence.
This content, previously submitted to law enforcement in the context of unwanted contact and coercive behavior, cannot retroactively be reframed as protected intellectual property for the purpose of silencing survivor documentation.
Any takedown request targeting such material constitutes a strategic misuse of copyright law, not a legitimate rights claim.
These files were published strictly under academic Fair Use and Fair Dealing protections, as part of an ethics-based documentation series. This takedown is not a valid copyright dispute, but a coercive response to institutional criticism.
Attempts to assert copyright over police-submitted evidence constitute a serious ethical and potentially legal breach. Such actions may be interpreted as obstruction of justice and retaliation against protected reporting
This is not copyright protection. This is reputational panic, disguised as a takedown notice.
The content was non-commercial, already submitted to Queensland Police (QPS) and regulators under official case IDs. Its removal constitutes an attempt to suppress documented harms rather than enforce legitimate rights. Misusing copyright mechanisms in this manner may qualify as a form of strategic litigation against public participation (SLAPP).
My publication falls squarely within the thresholds of:
Australian Copyright Act 1968 – Sections 41 & 42 (Fair Dealing)
U.S. Copyright Law – §107 (Fair Use)
International norms protecting public interest commentary and trauma documentation.
I have submitted a formal counter-notice. As per standard procedure, Google has forwarded the takedown request to the Lumen Database, where it is now publicly visible as part of platform transparency archives.
View takedown request on Lumen
If harassment persists, I reserve the right to escalate this matter to ethics boards, international legal monitors, and public interest watchdogs tracking strategic censorship and retaliatory misuse of institutional tools.
Any misuse of personal information obtained via counter-notice or takedown responses will be treated as further coercive harassment and may be reported to law enforcement under digital harm and privacy abuse frameworks.
No individual has the right to suppress survivor-led documentation solely on the basis of personal discomfort — especially when such material pertains to evidence already submitted to law enforcement.
Note on Naming:
The subject of these verses is identified by name due to the severity of the public threats made during that period.
Naming is not intended to humiliate, but to preserve the integrity of the record and reflect the seriousness of the documented behavior.
While the individual has since responded publicly, the response has not addressed the core evidence. In such cases, visibility remains necessary. Selective rebuttal is not accountability.
Full evidence archive submitted to QPS, TEQSA, AHRC, and Ethics Australia: View here.
Read the full series
- Entry 1: The Man Who Taught Me Ethics by Failing All of Them
- Entry 2: The Disappearance of the Public Poet
- Entry 3: The Hanging Tree Case Study
- Entry 4: Hidden Like Accountability
- Entry 5: The Collapse of Assumptions
- Entry 6: The Ethics of a Tinder Bio
- Entry 7: How He Ate Told Me Everything
- Entry 8: What Makes a Scholar Dangerous
- Entry 9: Fragment of Life, Fragment of Accountability
- Entry 10: Anatomy of Disappointment
- Entry 11: Legal Defense Challenges: A Framing Statement
- Entry 12: Six Years After Ronell – What Academia Still Doesn’t Get
- Entry 13: QUT and The Man Who Raped Me
- Entry 14: Why Sarcasm Toward Institutions Can Backfire
- Entry 15: P*ssy or Toxic Masculinity?
- Entry 16: Who is Your Favorite Comedian?
- Entry 17: And What is Your Favorite Song?
- Entry 18: Grant Proposal — Narrative Ethics as Survivor-Led Forensics
- Entry 19: The Coward Behind the Clone
- Entry 20: [URGENT HIRE] CRISIS COMMUNICATIONS SPECIALIST
- Entry 21: [URGENT] Legal Counsel Needed for Complex Reputation Rehabilitation
- Entry 22: YOU’RE AN ABUSER. STOP CONTACTING ME
- Entry 23: Seeking Counsel for a Fallen Academic
- Entry 24: Internal Legal-PR Briefing
- Entry 25: For Journalists – Legal & Ethical Clearance Summary
- Entry 26: Symbolic Prostitution, Transactional Intimacy, or Just a “Loan”?
- Entry 28: Why He Simply Cannot Shut Up
- Entry 29: Forensic Commentary on “LARGE Language Muddle”
- Entry 30: Don’t Just Threaten My Future. Because I’m Going To Archive Your Present
- Entry 31: Open Letter to the Person Who Tried to Break Me with Defamation
- Entry 32: Defamation, Harassment, Doxxing Class 101
- Entry 33: Confidential Crisis Recovery Proposal
- Entry 34: Forensic Behavioral-Somatic Report
- Entry 35: Forensic Commentary on the Tattoos
- Entry 36: QUT and the Abuser They Once Had
- Entry 38: When Poetry Becomes Revenge Porn
- Entry 40: A Man Built for Applause, Not Accountability
- Entry 41: Neurobehavioral Addendum
- Entry 43: Why Does It Sound Like a War Metaphor?
- Entry 44: Forensic Commentary on Racialized and Fetishizing Language in “Hidden Like Rice”
- Entry 45: Public Misuse of Former Academic Affiliation
- Entry 46: The Two Things That Didn’t Leave a Bad Impression
- Entry 47: When Affection is Just an Alibi (A Bundy-Inspired Reflection)
- Entry 48: Humbert, Lolita, and the Fetish of Fragility
- Entry 49: The Fetish of Smallness as Symbolic Violence
- Entry 50: Motif Risk Analysis
- Entry 51: To Johnston (you are here)
- Entry 52: Can an Abuser Be a Good Father?
- Entry 53: Who Protects the Children?
- Entry 54: From Blackmail to Children
- Reflection: The Miscalculation
(More entries coming soon)
→ [Back to Start: Introducing Mr. J, a Former Professor Series]
© 2025 Linh Ng. All rights reserved.
This publication is intended for educational and reflective purposes only.
Sharing the original link is welcomed and encouraged.
Please do not reproduce, redistribute, or translate this content — in whole or in part — without written permission.
This piece reflects both lived experience and critical analysis. It is not meant to be detached from its author or reframed without context.
Misuse or decontextualization may lead to formal clarification or takedown requests.
This work has been reviewed and quietly followed by scholars, educators, and ethics professionals across multiple sectors.
If your institution is engaging in critical discourse around narrative justice, symbolic coercion, or representational ethics, feel free to connect via Substack DMs or formal channels.
A regulatory case regarding this matter has already been classified under a protected status within national education integrity systems.
Should any reputational countermeasures or distortions arise, I reserve the right to publish the documented timeline, behavioral patterns, and contextual metadata.
All relevant documentation has been submitted through formal legal and regulatory pathways.
Photo cover by Markus Wrinkler via Unsplash